Your Digital Legacy,
Secured Forever.
Hardware-backed cryptographic vault. Autonomous unlock.
Blockchain-powered digital inheritance.
Digital Assets Disappear.
Centralized Systems Fail
LastPass, Uber, T-Mobile — billions of records leak every year. Even your password managers get hacked. Single server = single point of failure.
Death = Data Loss
Over $140 billion in crypto is permanently inaccessible. When the owner dies, digital assets — passwords, wallets, documents — are lost forever.
Current Tools Fall Short
Either you trust a centralized authority (1Password, Bitwarden), or struggle with complex technical setups (multisig).
Four-Layer Architecture
Physical hardware + context-aware key derivation + built-in crypto wallet + smart contract inheritance
Dual HID Device
Context Vector
No password needed
Zero-Knowledge
Wallet = Contract Owner
Blockchain timer
Unlock IPFS CID
their own key
securely transferred
Eight Security Layers
Context Vector
HKDF-SHA256 + Fuzzy Extractor derives keys from your environment. No password to remember — your location is your key.
Reed-Solomon ECC
Error-correcting codes over GF(2⁸) tolerate GPS drift. Your vault opens even if conditions shift slightly.
Shamir Secret Sharing
K-of-N threshold key splitting. No single point of failure — reconstruct the master key from any K shares.
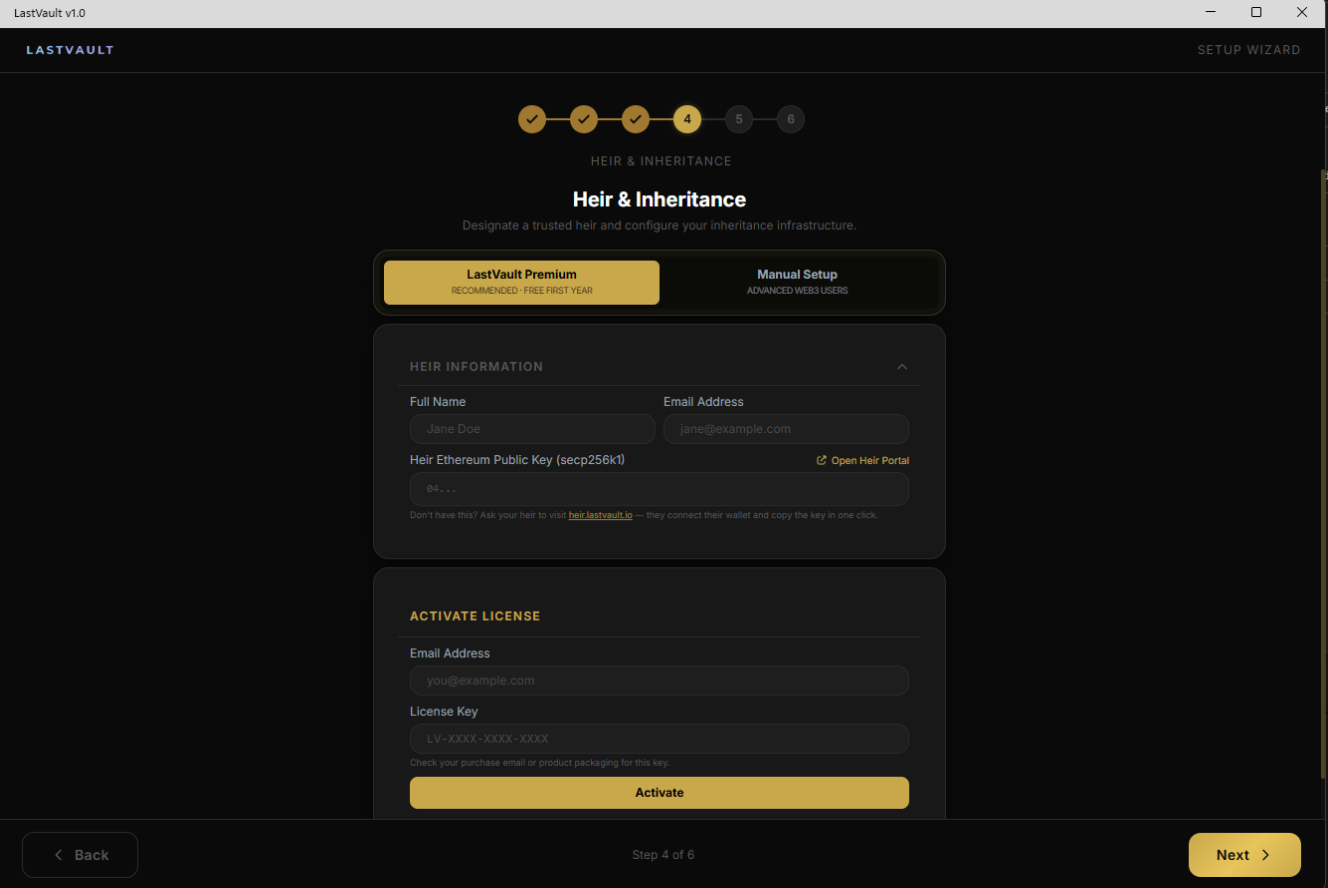
ECIES Inheritance
Heir's share encrypted with secp256k1 (Ethereum-compatible). Only they can decrypt when the time comes.
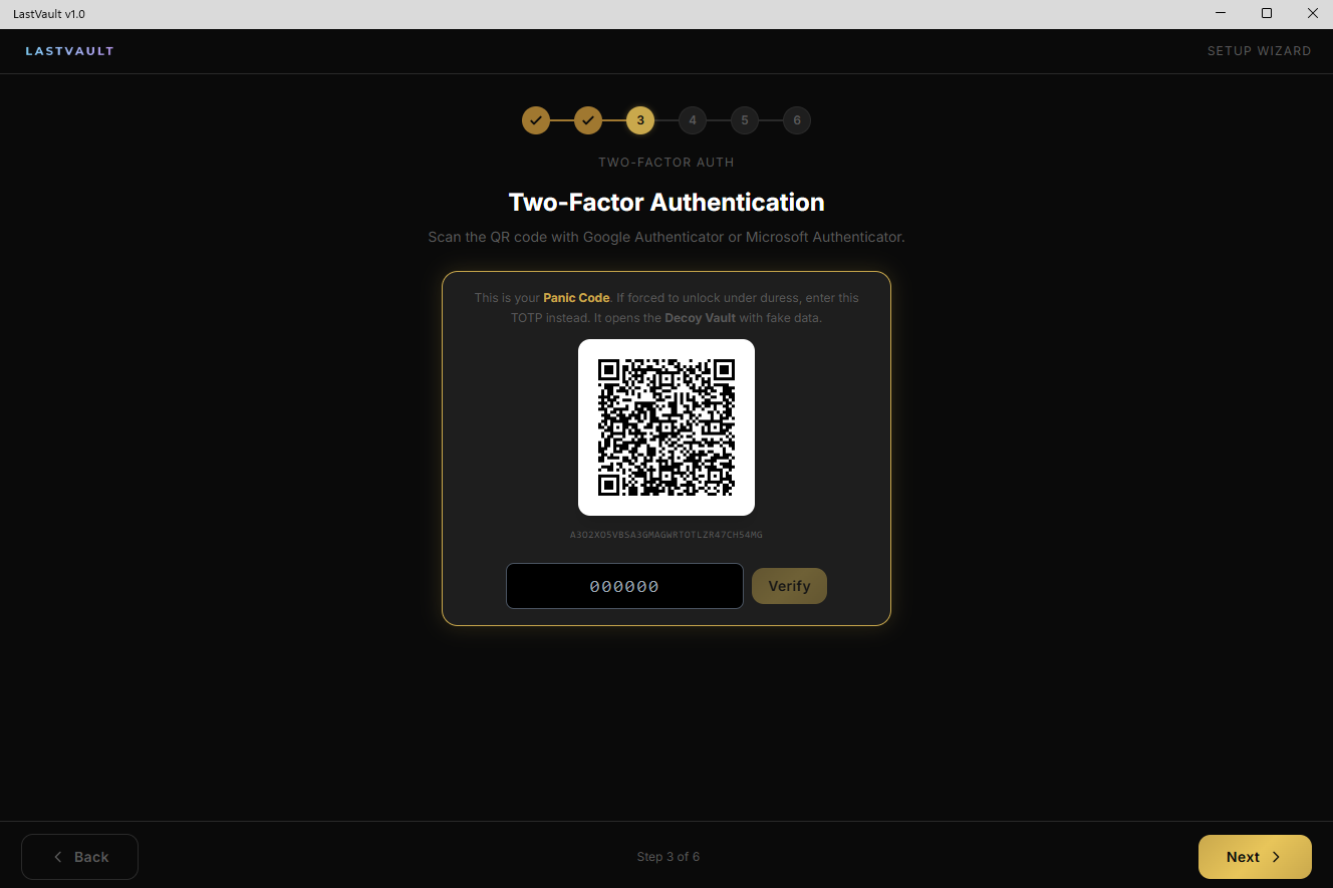
Decoy Vault
Under duress, enter a different TOTP code — a fake vault opens. The attacker never knows the real vault exists. Timing-safe comparison.
Zero-Knowledge
The server stores only encrypted blobs. No decryption capability on the backend — ever. Your keys never leave your device.
FIDO2 / CTAP2.1
The same USB device doubles as a FIDO2 security key. Dual HID composite: vault protocol + passkey authentication. ES256 via Secure Element, 100 resident keys.
Built-in Crypto Wallet
Send and receive ETH and ERC-20 tokens on Base L2 directly from your vault. Your wallet key is also your inheritance contract owner key — one key, complete control.
Why LastVault?
See how we compare to existing solutions.
| Feature | LastVault | Ledger | YubiKey | 1Password | Bitwarden | Casa |
|---|---|---|---|---|---|---|
| Zero-Knowledge Architecture | ✓ | N/A | N/A | ✗ | ~ | ~ |
| Hardware Security Key | ✓ | ✓ | ✓ | ✗ | ✗ | ✗ |
| Autonomous Unlock (no password) | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Blockchain Inheritance | ✓ | ✗ | ✗ | ✗ | ✗ | ~ |
| Dead-Man's Switch | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Decoy Vault (Plausible Deniability) | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Decentralized (no central server) | ✓ | ✓ | N/A | ✗ | ~ | ✓ |
| FIDO2 Passkey Support | ✓ | ✓ | ✓ | ✗ | ✗ | ✗ |
| File Encryption (not just passwords) | ✓ | ✗ | ✗ | ~ | ✗ | ✗ |
| Encrypted Vault + Password Manager | ✓ | ✗ | ✗ | ✓ | ✓ | ✗ |
| Built-in Crypto Wallet (Base L2) | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ |
Working Product. Right Now.
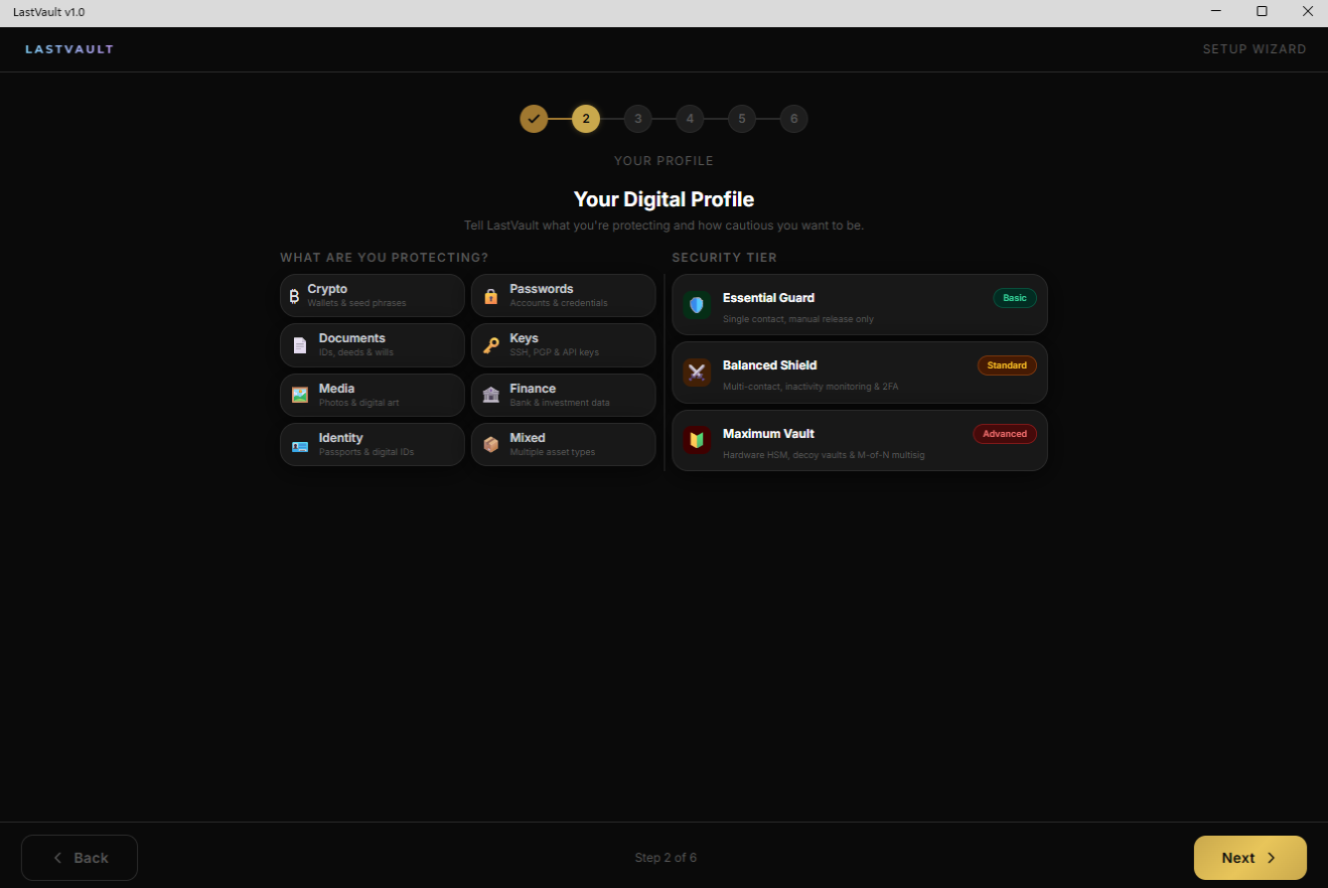
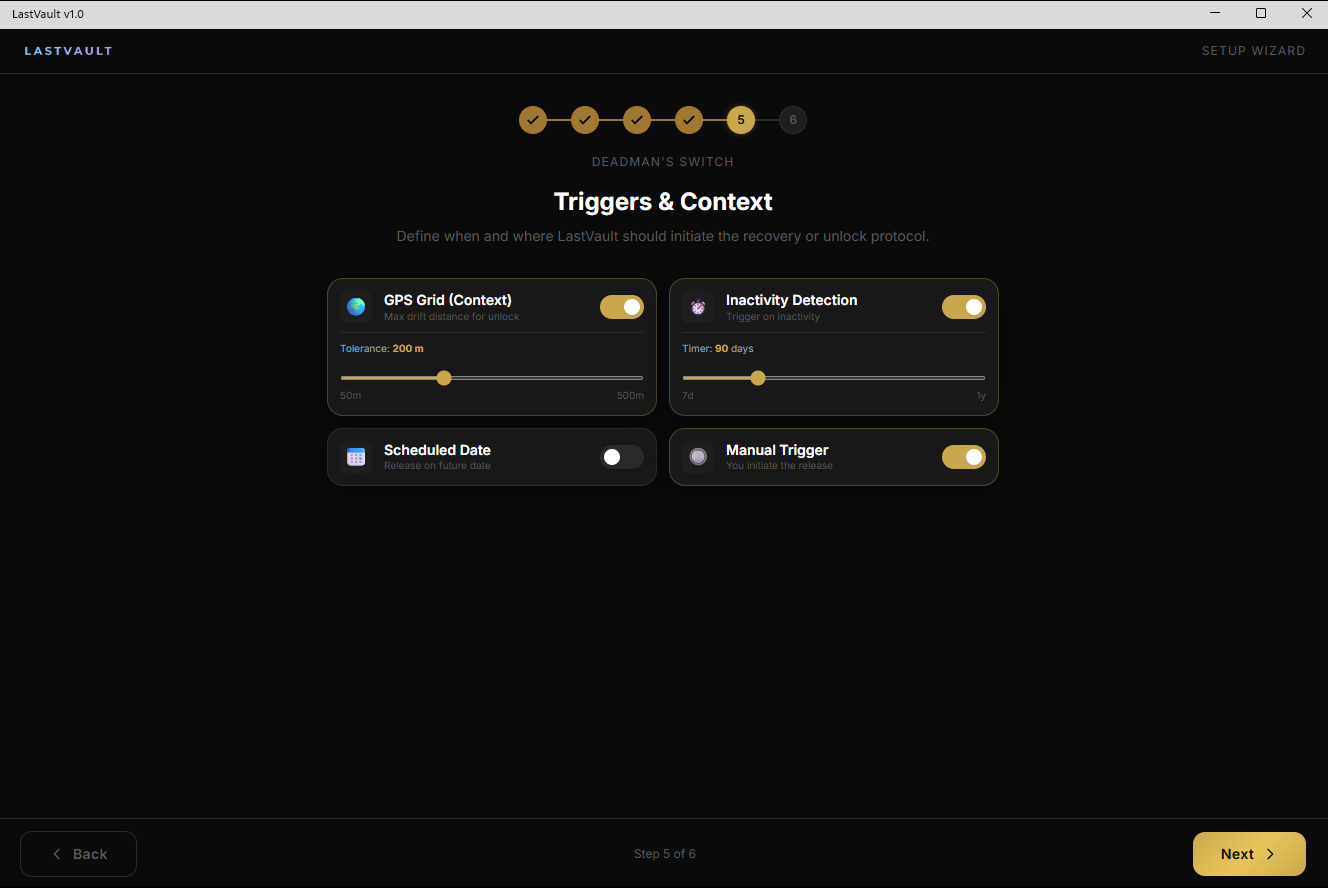
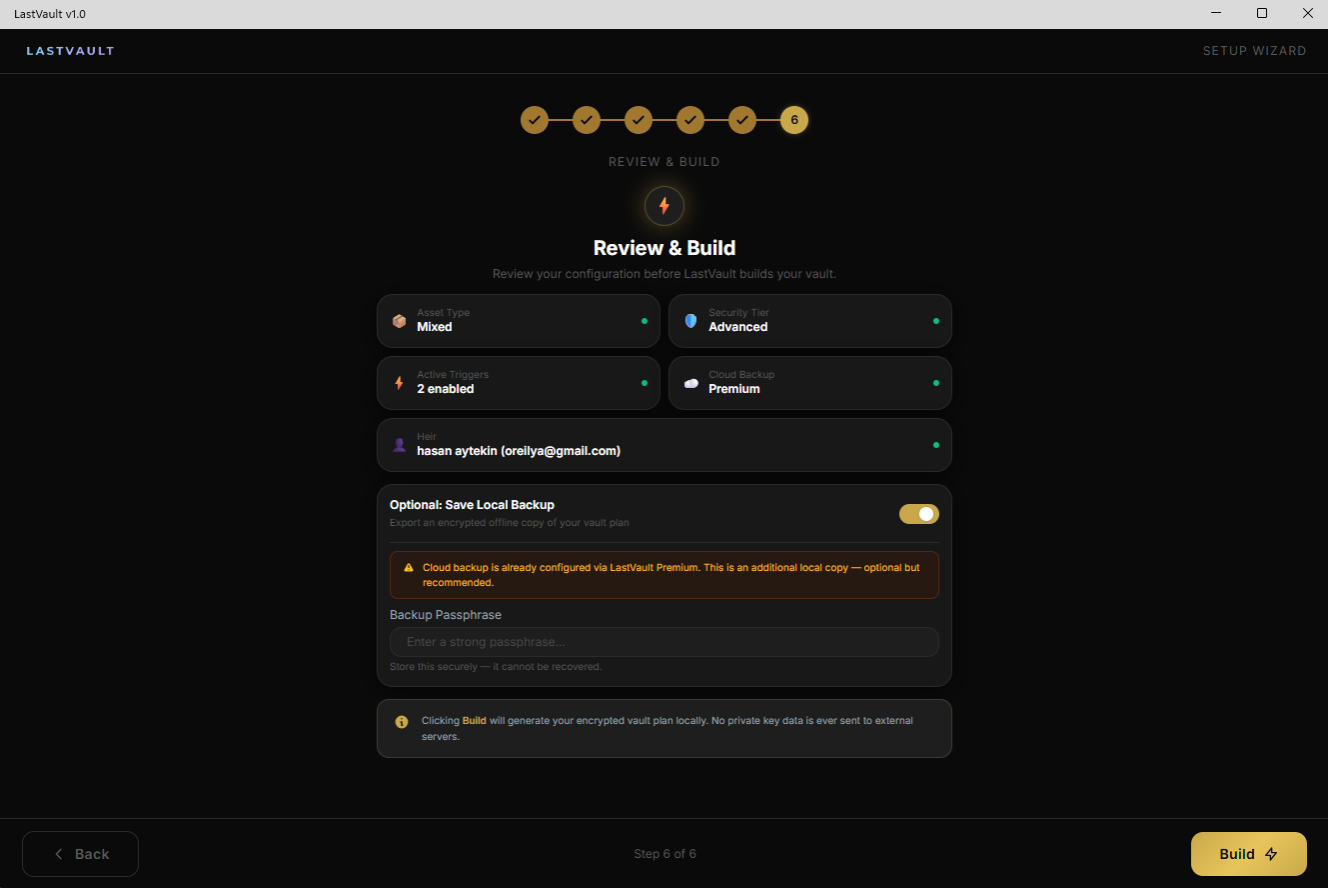
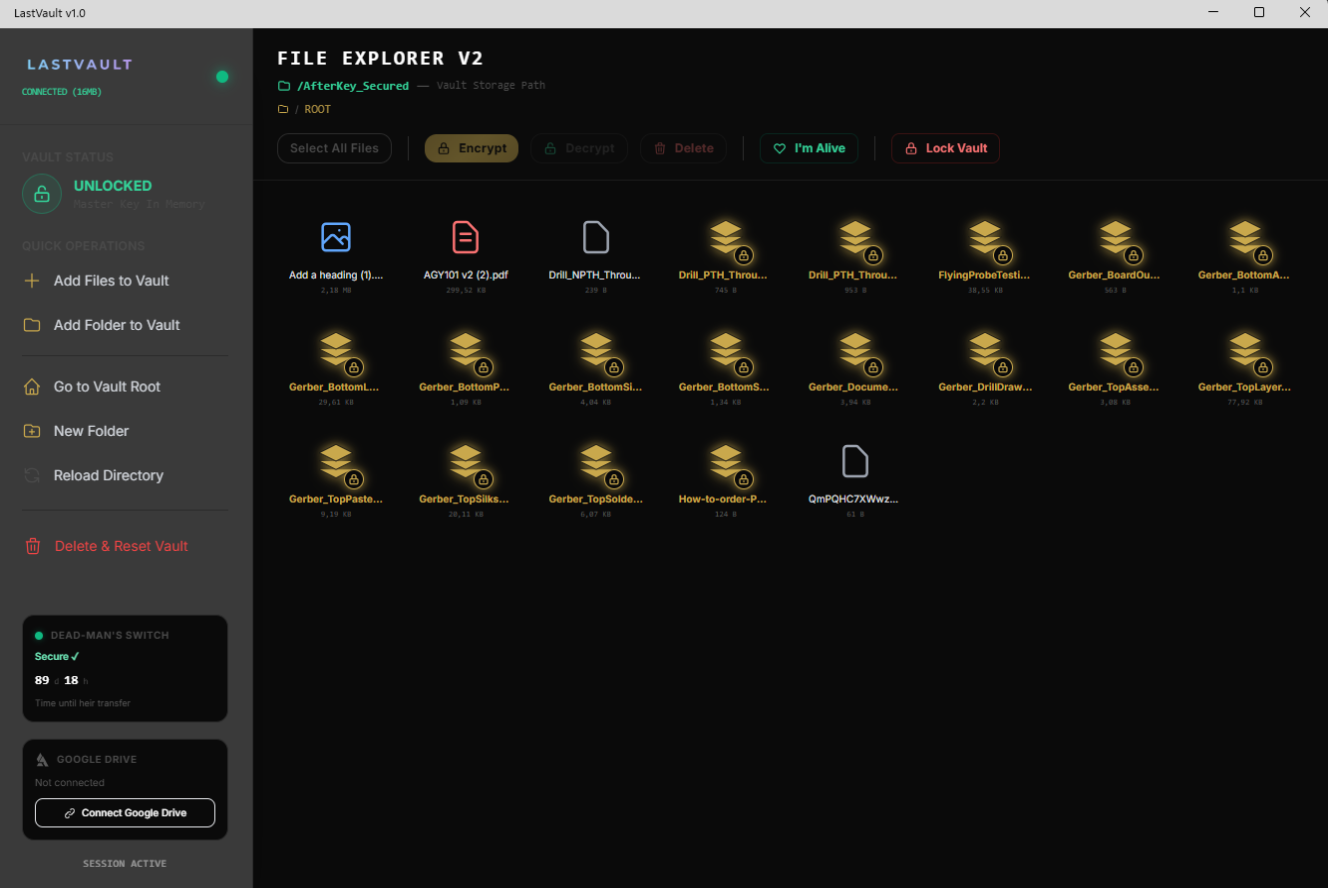
.NET 9 MAUI Blazor Hybrid — 6-step setup wizard, file manager, cloud sync, and autonomous unlock.
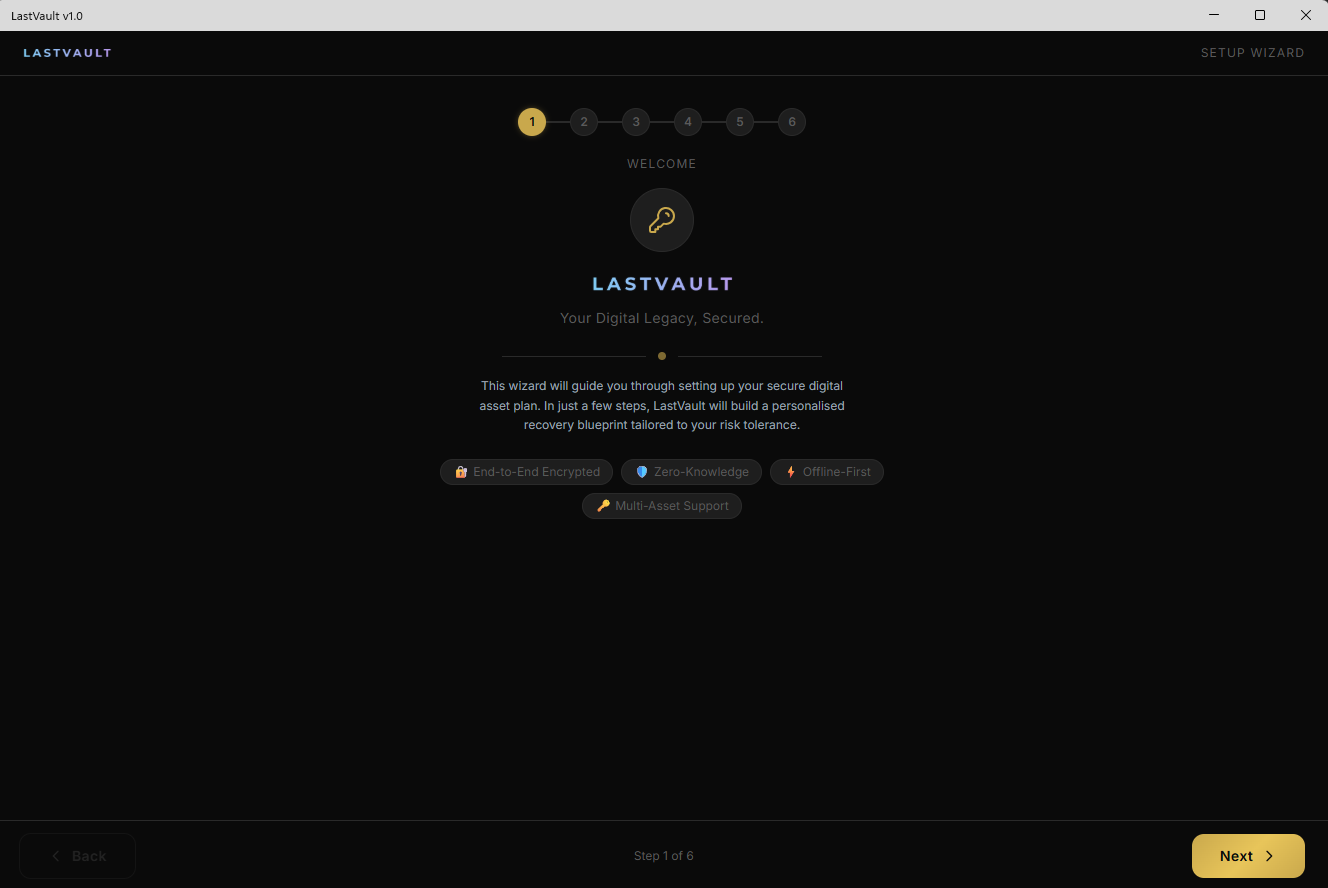
Welcome — Your Digital Legacy
6-step setup wizard with end-to-end encryption, zero-knowledge architecture, and offline-first design.
See It in Action
The LastVault hardware security key and desktop app — watch it in action.
Purpose-Built Security Key

Purpose-Built Security Key
A dedicated USB-A / USB-C hardware security module designed specifically for LastVault. Plug in, touch, done. Your physical key to the digital vault — no passwords, no seed phrases, no complexity.
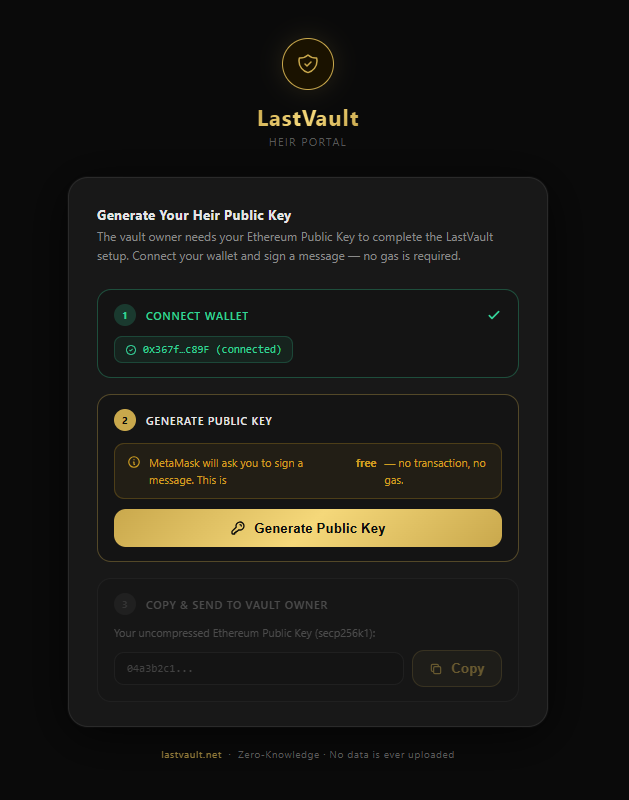
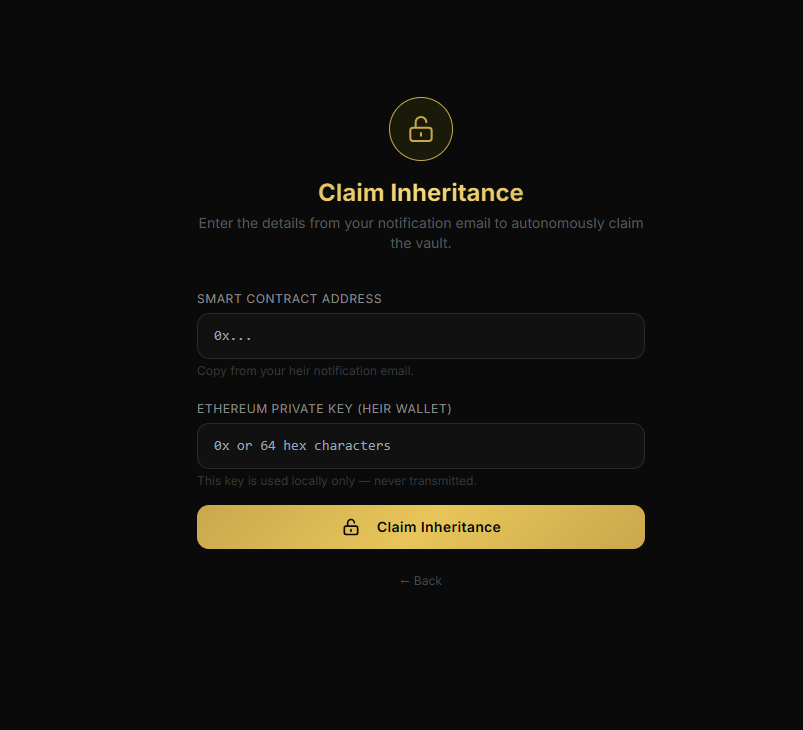
Your Legacy, Delivered
When the time comes, your heir receives a secure portal to claim their inheritance.
Smart Contract Triggers
After the configured inactivity period, the blockchain smart contract activates automatically.
Heir Gets Notified
Your designated heir receives access to the heir portal at heir.lastvault.io with their Ethereum key.
ECIES Decryption
The heir decrypts the vault using their private key. No central authority involved — fully decentralized.
Wallet & Assets Transferred
Digital assets — files, passwords, and the built-in crypto wallet (ETH + ERC-20 tokens on Base L2) — are securely delivered to the heir. Wallet key = contract owner key, so inheritance includes full wallet access.
Simple, Transparent Pricing
Start free. Upgrade when you need blockchain inheritance.
Free
- AES-256-GCM encrypted vault
- Context-aware autonomous unlock
- Decoy vault (plausible deniability)
- TOTP two-factor authentication
- Google Drive encrypted sync
- BYOK Web3 infrastructure
- Blockchain inheritance
- IPFS proxy upload
- Priority support
Premium
- Everything in Free, plus:
- Blockchain Dead-Man's Switch
- Smart contract inheritance
- IPFS encrypted backup (proxy)
- Heir portal access
- Hardware key integration
- Priority email support
- Built-in crypto wallet (Base L2)
- Future feature access
Frequently Asked Questions
Your encrypted vault is stored locally on your device. Optionally, you can sync an encrypted copy to Google Drive or IPFS. The server never has access to your decryption keys — zero-knowledge architecture means only you can read your data.
A Dead-Man's Switch monitors your activity. After a configurable inactivity period (default: 90 days), a blockchain smart contract triggers the inheritance flow — your designated heir receives the decryption key via ECIES, and your digital assets are securely transferred.
LastVault uses six layers of cryptography: hardware secure element, context-based key derivation (HKDF), error-correcting codes (Reed-Solomon), threshold key splitting (Shamir), asymmetric encryption (ECIES/secp256k1), and AES-256-GCM. There is no central server holding your keys — even if our backend were compromised, attackers would only find encrypted blobs.
Under duress (e.g. someone forces you to open your vault), you enter a different TOTP code. This opens a fake vault with decoy files. The attacker cannot detect that a real vault exists — this is called plausible deniability. The comparison is timing-safe to prevent side-channel attacks.
Yes. The LastVault hardware security key is required to use the application. It contains a dedicated secure element for cryptographic key storage and provides FIDO2/CTAP2 authentication. Your vault encryption keys never leave the device — this is the foundation of LastVault's zero-knowledge architecture.
LastVault includes a built-in EOA wallet on Base L2 (Coinbase Layer 2). You can send and receive ETH and ERC-20 tokens (USDC, WETH, DAI) directly from your vault. Your wallet private key is encrypted with your vault master key (AES-256-GCM) and zeroed from memory on vault lock. The same key serves as your inheritance smart contract owner — so when your heir claims the inheritance, they also gain access to your crypto assets.
The cryptographic core and protocol specifications will be published for independent audit and verification. We believe in transparency for security-critical software — trust, but verify.
Built by Engineers
A small, focused team combining cryptography, hardware, and software expertise.
Hasan Aytekin
Founder & Lead Engineer
Full-stack developer with expertise in .NET, cryptography, embedded systems, and blockchain. Designed the entire LastVault architecture from hardware to smart contracts.
Divara Teknoloji
Company
Divara Teknoloji ve Yazılım A.Ş. — a Turkish deep-tech startup focused on cryptographic security solutions and digital legacy management.
What's Next
Desktop App (MVP)
6-step wizard, encrypted vault, context-based unlock, decoy vault, Google Drive sync.
Hardware Security Key (PCB v1)
ESP32-S3 + Secure Element. KiCad schematics, prototype-ready design.
Web3 & Blockchain Integration
Built-in crypto wallet on Base L2, smart contract deployment, IPFS pinning, heir portal launch, Dead-Man's Switch on-chain.
Mobile App & Browser Extension
iOS/Android companion app, browser extension for password autofill, cross-platform sync.
Hardware Production & Enterprise
Mass production of USB security keys, enterprise licensing, compliance certifications.
Need Help?
Create a support ticket and we'll get back to you within 24–48 hours.
Or email us directly at hello@lastvault.io
My Tickets →